Whitepaper archive
Buyers checklist security first compliance and reporting
Ensuring and demonstrating compliance is a struggle for many enterprises. The work involved in adhering to rules and reporting requirements while avoiding penalties is growing, as employees gain more access to sensitive resourc...
2023 Buyers Guide: How to Vet Identity and Access Management Solutions
Whether you’re a security leader making the case to invest in new tools or an IT team member researching vendors, you could use unbiased advice on vetting Identity and Access Management solutions. That’s exactly what this eBoo...
Four Ways to Secure Identities as Privilege Evolves
Any user can become privileged in certain conditions. This includes everyday employees using business applications in which they can access — and take actions with — the resources attackers aim to exploit. And whether you’re a ...
Reinforce Least Privilege by Rethinking Identity Management
The definition of privilege is changing, and this changes everything. Identities of all types — not just IT team members, but any employees — are gaining access to sensitive data, infrastructure and systems that today’s attack...
4 Tips for Sales Teams to get more value from Slack
In this on-demand webinar, learn how, with Slack as your Digital HQ for Sales, your company can win more deals as a team, connect with customers to win, automate admin to focus on selling and integrate Slack with Sales Cloud.
Slack State of Work Report 2023
When Slack released its first State of Work report in 2019, the biggest issue facing workers seemed relatively simple: how to align effectively around their shared mission. But the world has changed radically in the four short ...
Southeast Asian Oil & Gas Giant Reduces the Attack Surface & Secures Operations with Claroty
This southeast Asian oil and gas industry firm’s security, engineering, and executive personnel all recognized that preserving the availability, integrity, and safety of its hydrocarbon production operations required a robust o...
Achieving Cyber Resilience
Achieving and maintaining cyber resilience amid the XIoT’s challenging security and risk conditions is far from impossible — but it does entail a robust set of requirements that simply cannot be satisfied by traditional solutio...
Running the numbers: the key to improve your business spend control
If you don’t know all your business spend numbers, you can’t control it. The truth is always in the numbers, but it also hides there – under a few mistakes, figures in the mileage logbook, behind missing auditing, or in cash tr...
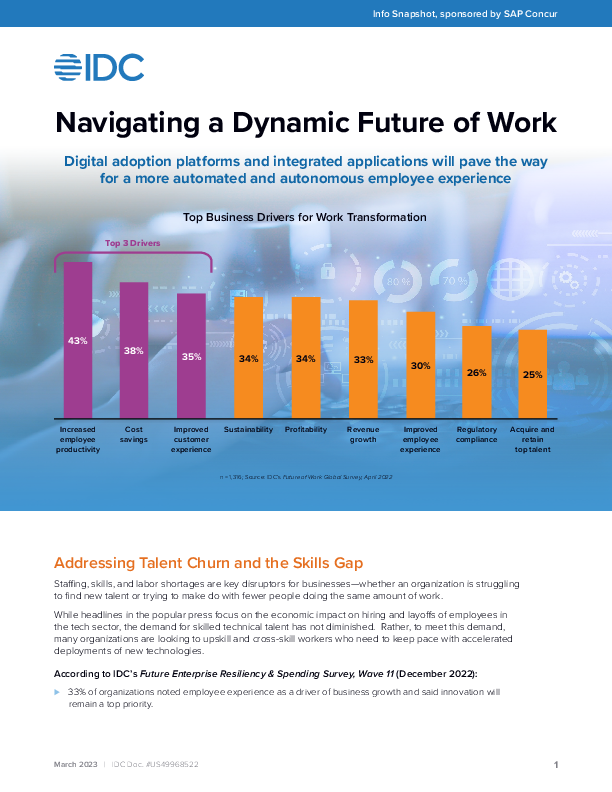
IDC Snapshot: Navigating a Dynamic Future of Work with Digital Adoption Platform
Staffing, skills, and labour shortages are key disruptors for businesses—whether an organisation is struggling to find new talent or trying to make fewer people do the same amount of work. Businesses left with fewer employees t...