Archivo whitepaper
The potential of payroll: Global payroll survey
ADP’s The Potential of Payroll is a study into the performance, resilience, and strategic contribution of payroll in today’s global business landscape, and how global payroll teams, systems, and processes are evolving to meet t...
Is your payroll keeping pace?
A direct consequence of all this transformation is businesses of all sizes – companies like yours – finding it difficult to keep pace with how quickly payroll and HR functions are evolving. It’s becoming clear: what got you to ...
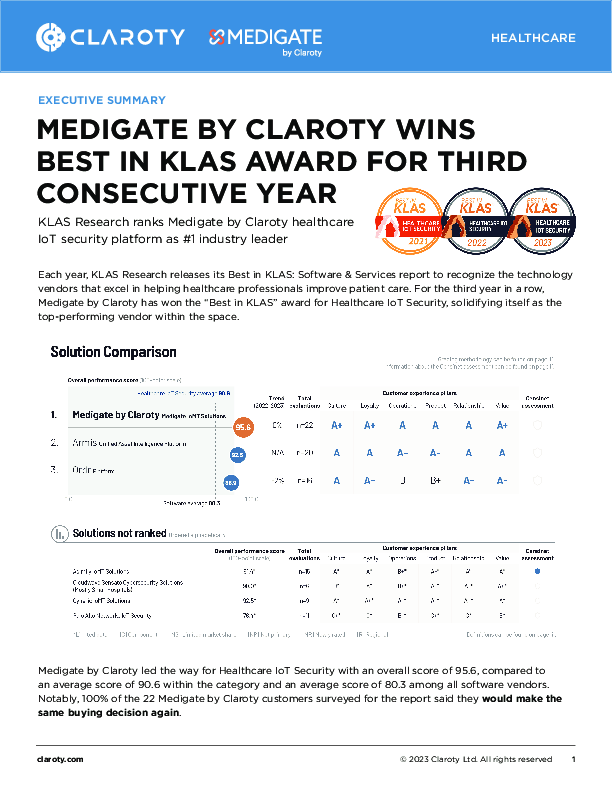
MEDIGATE BY CLAROTY WINS BEST IN KLAS AWARD FOR THIRD CONSECUTIVE YEAR
Each year, KLAS Research releases its Best in KLAS: Software & Services report to recognize the technology vendors that excel in helping healthcare professionals improve patient care. For the third year in a row, Medigate b...
Defending Australia's Critical Infrastructure from Cyber Attacks
As an increasingly complex and hostile environment builds around cybersecurity, Australia, along with the rest of the world must navigate how to defend against cyber threats while maintaining resilience and growth. In a recen...
Four Technologies To Future-Proof Your Workplace
The future of work is now. In the UK, fully remote and hybrid knowledge workers will represent 67 per cent of the workforce by the end of 2023. By facilitating modern working with the right technology and culture, organisation...
Visibility & Insights and Anomaly & Threat Detection
There’s a surge of connected medical devices and the Internet of Medical Things (IoMT), and it’s a massive challenge for healthcare IT, BioMed, and security teams. Unlike those found on other IT networks, managing and securing ...
Guía para la adquisición 2023: Cómo examinar las soluciones de gestión del acceso y la identidad
Tanto si es usted un responsable de seguridad que defiende la inversión en nuevas herramientas como si es un miembro del equipo de TI que está comparando proveedores, le vendrá bien un asesoramiento imparcial para examinar las ...
Guide d’achat 2023 : Comment examiner minutieusement les solutions de gestion des identités et des accès
Que vous soyez un leader de la sécurité qui demande à investir dans de nouveaux outils ou un membre de l’équipe informatique qui recherche des fournisseurs, vous pouvez utiliser des conseils impartiaux sur l’examen minutieux de...
Cuatro formas de proteger las identidades a medida que evolucionan los privilegios
Cualquier usuario puede tener privilegios si se cumplen determinadas condiciones. Por ejemplo, los empleados cotidianos que utilizan aplicaciones empresariales en las que pueden ver y gestionar los recursos que los atacantes pr...
Refuerce el mínimo privilegio replanteándose la gestión de la identidad
La definición de privilegio está cambiando, y esto lo cambia todo. Identidades de todo tipo (no solo miembros del equipo de TI, sino cualquier empleado) acceden a datos, infraestructuras y sistemas sensibles que los atacantes d...