Archivo whitepaper
Buscar
documentos disponibles actualmente: 11937
Temas más recientes:
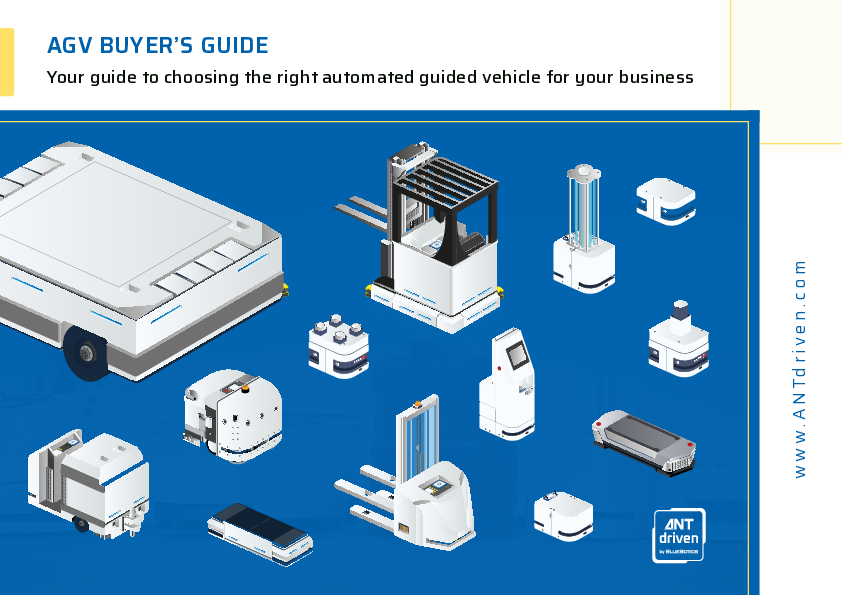
AGV BUYER’S GUIDE: Your guide to choosing the right automated guided vehicle for your business
Ver libro electrónico
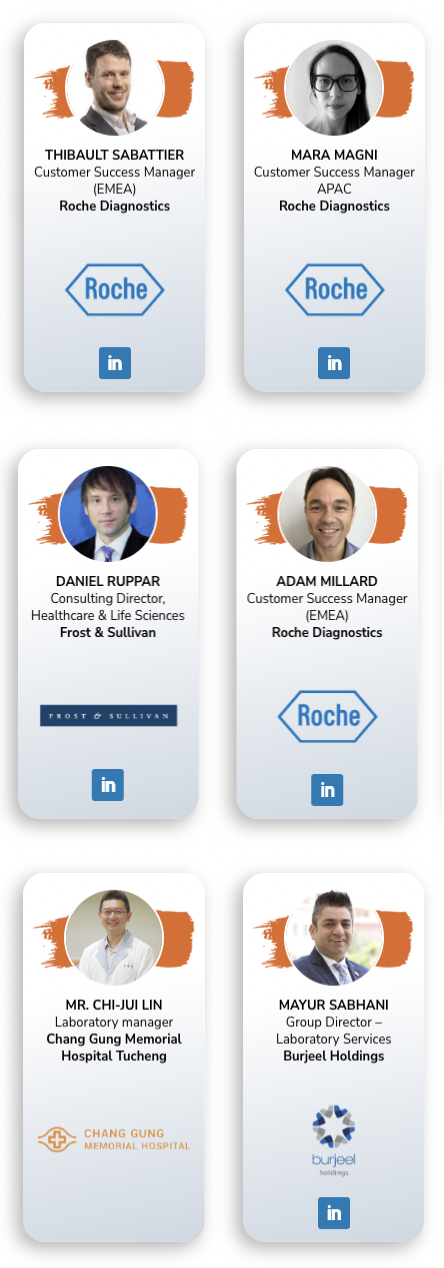
Achieving Operational Excellence within your Laboratory via Integrated Digital Solutions
Ver el vídeo
Stay Ahead of Year End Overload: Streamline Reporting With Automated Disclosures
Ver el seminario web a la carta
Encuesta sobre IA, fraude y delitos financieros 2024: El rol de la IA en la perpetración y la lucha contra los delitos financieros
Ver whitepaper
Suscríbete a nuestra newsletter
Las noticias más importantes gratis por correo electrónico