Hvidbogsarkiv
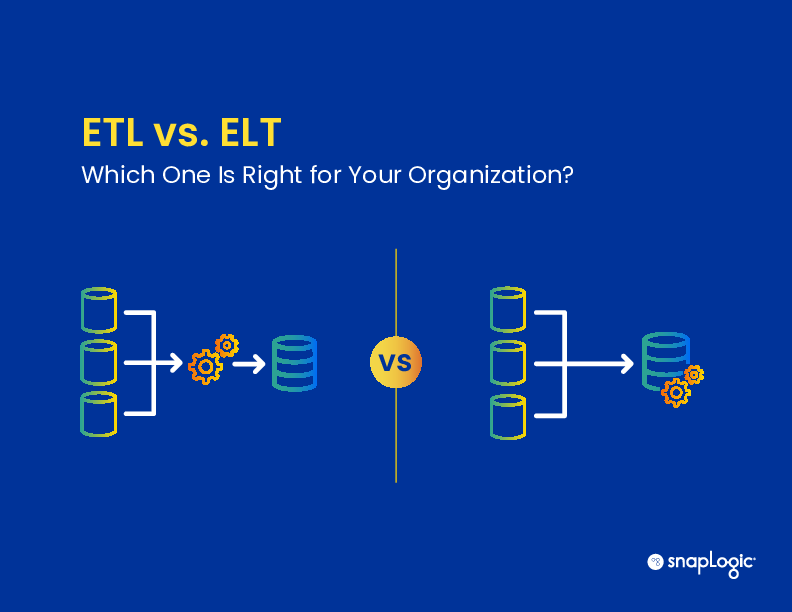
ETL vs ELT: Which One Is Right for Your Organization?
As part of the data integration workflow, data transformation is the process of preparing, formatting, and joining data for placement in a data repository or data warehouse for analytics. For decades, the data transformation me...
Magic Quadrant for Integration Platform as a Service
Generative AI (GenAI) has heightened awareness and need for AI-augmented integration delivery. Integration specialists, business analysts and line of business workers can reference this report to evaluate which integration plat...
Generative AI in Action: Adoption Trends, Emerging Use Cases, and Tips for IT Leaders
Every once in a while, we encounter a piece of technology that transforms society. Looking back throughout history, examples of this kind of paradigm-shifting transformation include industrialized manufacturing, television, per...
The Ultimate API Management Buyer's Guide
This buyer’s guide was created to help anyone evaluating an API management solution for their iPaaS and data integration needs. It is designed to help the buyer identify potential pitfalls and to have the tools to successfully ...
Subscribe to Safety: How to grow your private security firm and provide peace of mind with body cams
If you own or work in a private security firm, you have plenty of worries - everything from rising public aggression to cut-price competitors. Outdated approaches to technology only compound these concerns. This decision guid...
Rimmel sees a 44% sales lift from Bazaarvoice's Influenster community
To quantify the importance of peer-to-peer recommendations in the purchasing decisions of consumers, Bazaarvoice partnered with market research company IRI to measure the impact of ratings, reviews, and visual social content in...
Kraft Heinz earns 39 million impressions from the Influenster community.
Grocery shoppers are always hungry for new flavors from familiar food brands, which is why Kraft Heinz regularly launches new products. When the global company recently created eight new flavors of salad dressings, it knew gett...
Petco’s Spotted sampling program drives 48% revenue increase on sampled products
Since 2005, Petco’s dedication to supporting the overall health and wellness of pets has been supported by a suite of Bazaarvoice solutions, including Ratings & Reviews and Questions & Answers. These services have allow...
Buyer's guide: Find the perfect product sampling partner
Product sampling is key to acquiring the user-generated content you need to fuel your shopper’s journey and impact the full customer funnel. But it can be tricky to get right. Without proper planning and support, marketing team...
6 ways to launch your product with a bang
In the past, product launches relied on in-store activations. Now, virtual displays and digital content are crucial for success. Brands must create seamless experiences across online and offline channels. The key to any produc...