سجل المستندات التعريفية
With Cloudya you get one smart cloud communication platform that does it all!
Are you ready for flexible communication from the office, at home, or on the go No matter if you are looking for simplified voice calling, easy video conferencing, or seamless integrations for your CRM and collaboration tools...
A Buyer’s Guide to ESG Data Management Software
Environmental, social and governance (ESG) issues have become more complex and multifaceted than ever before. At the same time, they continue to ascend on board and leadership agendas. As forward-thinking corporations fold ESG...
Annual General Meetings Trends for board governance in the Benelux
The most well-known event in the communication between boards of directors and shareholders of listed companies is the annual ritual Annual General Meetings (AGM). This whitepaper by Diligent provides an overview of trends in ...
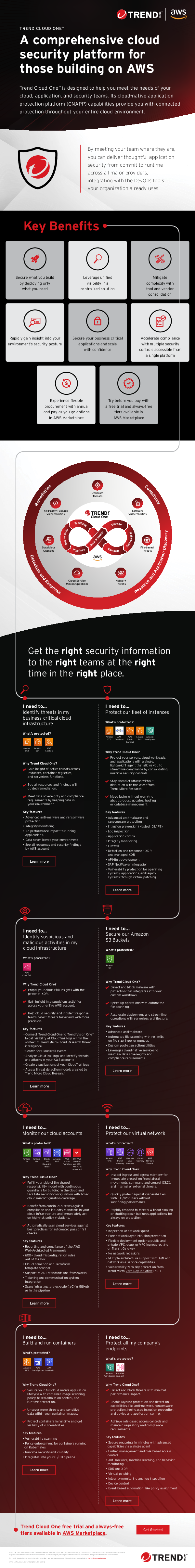
A comprehensive cloud security platform for those building on AWS
Trend Cloud OneTM is designed to help you meet the needs of your cloud, application, and security teams. Its cloud-native application protection platform (CNAPP) capabilities provide you with connected protection throughout you...
Ransomware: 6 Capabilities Enterprises Need for Rapid Recovery
Enterprises can’t prevent a cyberattack, but they can take steps to effectively protect their data when an attack occurs. This white paper features six best practices you need to know about ransomware recovery.
2023 Data Protection Trends Exec Brief
Learn how 4,200 business and IT leaders address their IT and data protection strategies. Download this brief and learn from their shared insights.
Ransomware Trends Executive Summary
Ransomware is a problem that everyone has but no one wants to talk about publicly. We asked 1,200 IT leaders from organizations of all sizes to open up and tell us what it was like to survive a cyber attack.
Veeam Data Platform Enterprise Demo
The Veeam® Data Platform ensures organizational resiliency through data security, data recovery and data freedom for your hybrid cloud. Watch this new 8 minute demo video to learn more.
2023 Cloud Protection Trends: Executive Brief
In the new 2023 Cloud Protection Trends report, 1,700 unbiased IT leaders were surveyed about their perspectives, methodologies and responsibilities in protecting, securing and managing their cloud hosted data. This exclusive ...
Enterprise Buyer’s Guide for data protection
Are you and your team considering all the facets of a new data management strategy? This 451 Research Pathfinder Report provides direction into what capabilities you should look for in a hybrid IT solution and outlines the que...