Arquivo de Documentos Técnicos
Comprehensive Cybersecurity Defenses for Content Delivery
Cyber-criminals are increasingly sophisticated and targeted in their attacks. If you are in charge of ensuring the security of your company’s website, it has not been easy going as these notable security incidents reveal: • Sa...
The IT Security Enforcer’s Advisory on Managed Security Services Models and Execution
Security is about protection, and in the enterprise IT environment, that means protection of a burgeoning array of physical and digital objects. Most objects, or property, within an enterprise can also be defined as assets, mak...
The Evolving Cybersecurity Landscape in the MECA Region
Tata Communication's Avinash Prasad on Regional Nuances in 2018 Organizations in the Middle East and Central Asia are beginning to respond to the nuances of the evolving threat landscape in the region, says Avinash Prasad,...
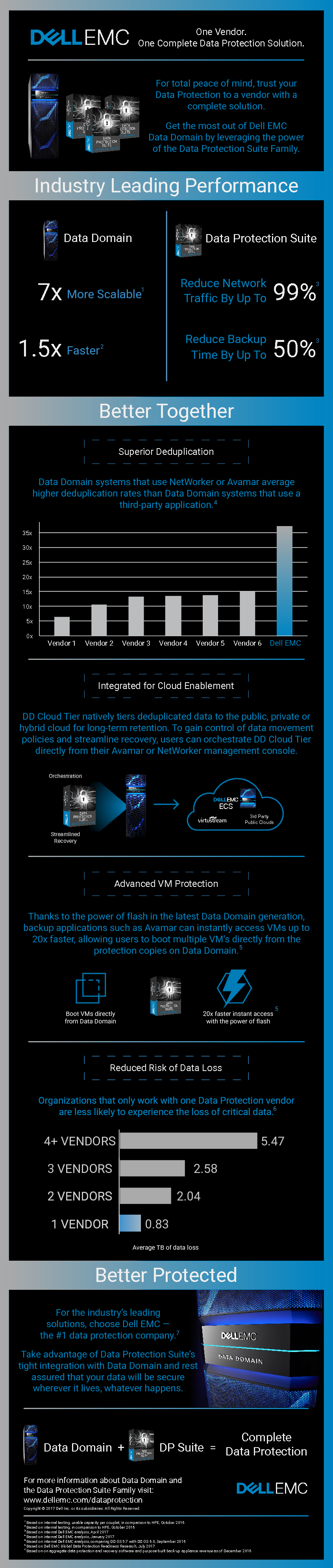
One Vendor. One Complete Data Protection Solution.
Protect your data everywhere, from physical to virtual to cloud Lower your cost-to-protect and protect more data – from any threat – with cloud-enabled Dell EMC Data Protection solutions powered by Intel® Xeon® processors. Arc...
Understanding data lakes and security
The cyberthreat landscape has never been more complex and fast moving. This means any new technology that can be used in the fight against cybercrime can bring real value to the security operations centre (SOC). Given how orga...
How to build a SOC with limited Resources
The purpose of this white paper is to show you how you can successfully build a SOC, even with limited resources. The paper first explains the basics of the Cyber Attack Lifecycle and the need to address it through the Threat L...
Machine learning and artificial intelligence in cybersecurity
One of the most common problems for enterprise security teams is how to respond effectively to the sheer volume of alarms they face every day. With so much noise, it can be hard for personnel to filter out false positives and f...
Next-generation ransomware
In recent years, ransomware has grown very quickly from relative obscurity to become one of the greatest cybersecurity risks facing organisations today. Ransomware is not a new type of threat: it’s been around in its current fo...
User and Entity Behaviour Analytics - Protecting your organisation from within
When it comes to detecting and responding to threats, many organisations focus their efforts on potential breaches from external sources. The truth is, an organisation’s largest security threat often lies within its own network...
Relay™ communications hub data security
The Relay™ communications hub lets you modify and improve your print communications as well as getting you ready for sending digital communications. Minimise disruption by working seamlessly with your existing systems. This do...